
Data Security Posture Management (DSPM)
Data Security Posture Management (DSPM) is a modern approach to identifying, monitoring, and securing sensitive data across cloud, SaaS, and data platforms. Unlike legacy tools, DSPM focuses on the data itself—where it resides, who has access, how it is being used, and whether it complies with privacy and security policies. By doing so, organizations can reduce risk, prove compliance, and protect business-critical assets. GoTrust DSPM provides continuous data security posture management solutions that automatically discover sensitive information, classify it, and remediate exposures with audit-ready evidence.

Why Data Security Posture Management Matters ?
Data is now distributed across hybrid cloud, SaaS, and on-prem systems. Without visibility, organizations risk compliance violations, insider threats, and data leaks.
What is data security posture management?
It’s the discipline that ensures organizations know where their sensitive data lives, how it flows, and how to enforce the right controls—without slowing down business. GoTrust addresses this challenge by unifying data visibility, compliance enforcement, and automated remediation in one platform.
End-to-End Data Exposure Management
Take command of your entire data landscape with our unified platform. Ensure compliance, mitigate risks, and empower your organization through unparalleled data visibility and control.
01
1. Data Discovery & Visibility
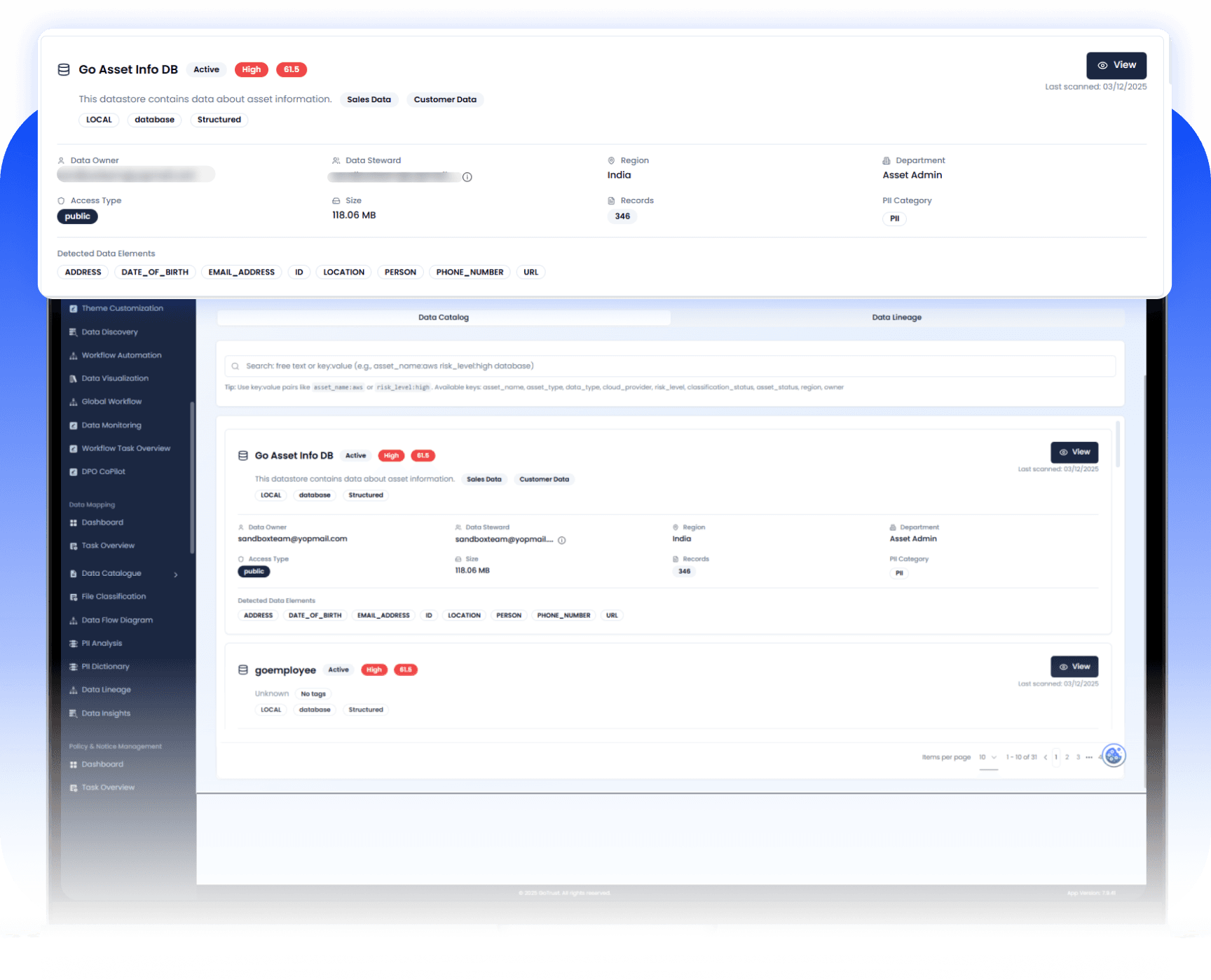
Ability to automatically discover structured and unstructured data across cloud, SaaS, on-prem, and hybrid environments.
Provides a complete inventory of data assets including shadow or unknown data stores.
Ensures organizations always know where sensitive data resides.
Continuous discovery is foundational because without visibility, risk cannot be managed.

02
Sensitive Data Classification & Contextual Understanding
Classifies data based on sensitivity (PII, PCI, PHI, financial, IP, etc.).
Applies regulatory mapping (GDPR, HIPAA, PCI DSS, etc.).
Uses ML or pattern detection to improve accuracy and reduce false positives.
Helps prioritize protection and enforce correct policies based on business and compliance risk.
03
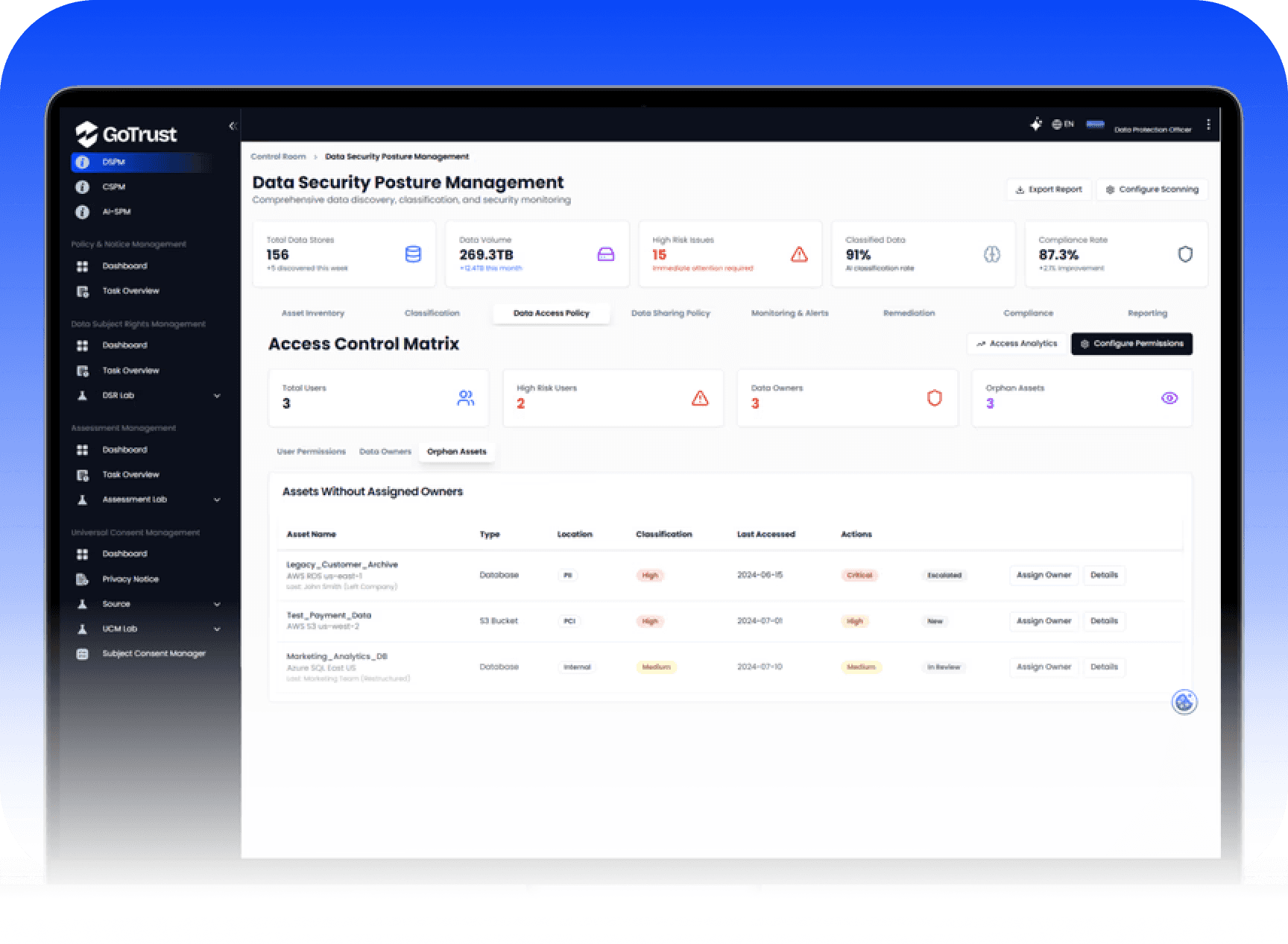
Access Governance & Risk Analysis
Evaluates who has access to data and whether that access is appropriate.
Detects over-privileged users, public exposure, and misconfigurations.
Provides risk scoring based on sensitivity + exposure + usage patterns.
Enables least-privilege enforcement and reduces breach attack surface.


04
Continuous Monitoring, Detection & Alerting
Tracks data movement, access behavior, and policy violations in real time.
Detects anomalies, suspicious access patterns, or insider threats.
Integrates with SIEM, DLP, and security monitoring ecosystems.
Converts DSPM from a periodic audit tool into a real-time security control layer.
05
Automated Remediation & Policy Enforcement
Provides actionable remediation such as access revocation, encryption, masking, or deletion workflows.
Enables automated or workflow-driven response to posture gaps.
Supports compliance reporting and audit readiness.
Drives business value by reducing manual effort and closing risks faster

Operationalization & Collaboration:
Integrating Governance into the Business
Move beyond mere detection. Operationalize data governance with cross-team workflows and seamless integration into your existing security and IT infrastructure.
Workflow & Collaboration
Cross-Team Collaboration: Facilitate Cross-team collaboration with shared dashboards, task assignment, and violation commenting for Data Owners, Security Teams, and IT Operations.
Automated Workflow Integration: Seamlessly integrate governance processes with your existing security tools via Automated workflow integrate with ITSM/SOAR tools like ServiceNow and Jira, enabling automatic ticket creation for violations, owner assignment, and status updates.
Testing & Deployment
Sandbox Environment: Utilize a Sandbox testing environment to safely simulate policy changes, test new PII definitions, and validate auto-remediation actions before deploying them to production.
Compliance & Reporting: Audit-Ready Evidence
Maintain continuous compliance by generating undeniable, audit-ready evidence for regulators and internal auditors.
Compliance Framework Mapping
Service Agreement Summary This agreement is made between NovaTech Solutions ("Provider") and Skybridge Enterprises ("Client") on March 15, 2025. The Provider agrees to deliver customized AI-driven data solutions, including predictive analytics and automated reporting, to the Client for a duration of 12 months. Key Terms:
Business Requirement View
View violation list per compliance business requirement wise, making audits and regulatory reporting straightforward.
Evidence Generation
Automatically generate Audit-ready evidence in policy, violation, and remediation logs, providing immutable proof of compliance activities and risk mitigation measures for every decision and action taken on the platform.
Audit-Ready Evidence
Why GoTrust DSPM Data Security
Comprehensive Features to Secure Sensitive Data

Data-first approach
Protect sensitive data, not just infrastructure

Risk-based prioritization
Focus on the exposures that matter most

Cross-team collaboration
Privacy, security, and data teams working together

Sandbox Testing Environment
Safe, isolated environment for testing governance policies and discovery workflows.

Audit-ready evidence
Policies, violations, and remediation logs packaged for regulators
GoTrust is not just another tool it is a DSPM data security posture management platform that empowers organizations to move beyond reactive security into proactive resilience.
Discover everything we’ve created with you in mind
From smart tools to seamless design features, every detail is crafted to make your experience smoother, faster, and more impactful.
Immediate visibility into data sprawl
Faster detection and remediation of risk
Centralized governance across cloud and SaaS
Board-level reporting that translates security posture into business value
Key Benefits
Business Value Through Security and Compliance

Stronger protection
Prevent data leaks with DSPM security and risk-based prioritization.
Faster compliance
Exportable evidence packs for GDPR, HIPAA, PCI DSS, ISO 27001, India DPDPA, and more.
Reduced risk
Rapidly shrink the attack surface by eliminating shadow and overexposed data.
Operational efficiency
Automated workflows integrate with ITSM/SOAR tools like ServiceNow and Jira.
Who Uses GoTrust DSPM
Security leaders, IT teams, and compliance experts safeguarding sensitive data.
CISOs & Security Leaders
Real-time posture, ROI, and board-ready reporting .
DPO & Privacy Teams
Compliance oversight with audit evidence.
Data & Cloud Teams
Right-sized access and clean data zones.
Application Owners
Guardrails without slowing down delivery .

INTEGRATIONS
PRE–BUILT APIS WITH
300+ SYSTEMS, APPS and MODELS

GoTrust Knowledge Hub
Stay informed with insights, updates, and expert perspectives on data privacy, compliance, and digital trust.
Frequently Asked Questions (FAQ)
How is DSPM different from DLP or CSPM?
Will it slow down user workflows?
Can we create custom policies?
How do you ensure accountability?
What about scoping access?




Talk To Our Expert
Schedule a session with our team to see how GoTrust unifies consent, privacy automation, DSPM, and governance into one intelligent compliance platform.





















