Endpoint Discovery
Find. Classify. Protect. Sensitive Data Wherever It Lives.
Discover hidden sensitive data across every laptop, desktop, and endpoint in your enterprise — before a breach finds it first.
https://www.gotrust.tech
What Is GoTrust Endpoint Discovery?
In today's distributed work environment, sensitive personal and business data doesn't just live in servers and cloud repositories — it resides on thousands of employee laptops, desktops, and local workstations spread across your enterprise. Every untracked spreadsheet, unsecured document, or forgotten database file is a potential compliance violation waiting to happen.

GoTrust Endpoint Discovery is a powerful module within the GoTrust Data Privacy Compliance Platform that automatically scans, identifies, and classifies sensitive data stored on enterprise endpoints. By bringing full visibility to data that exists outside centralized repositories, GoTrust empowers your privacy, legal, and IT security teams to act with confidence — and stay ahead of regulatory requirements.
The Problem With Endpoint Data Blind Spots
Most organizations have a reasonable grasp of data stored in their central systems. But endpoint devices tell a very different story:
Employees routinely save copies of sensitive files locally for offline access
Legacy data lingers on devices long after projects have been completed
Shadow IT practices create untracked repositories of customer and employee data
Remote and hybrid work setups have dramatically expanded the endpoint surface area
Manual data audits are slow, expensive, and error-prone at enterprise scale
Without comprehensive endpoint visibility, your organization is making privacy compliance decisions based on incomplete data — creating significant exposure under GDPR, CCPA, HIPAA, PDPB, and other global regulations.
10%
10%
of data breaches involve endpoint devices
0M+
0M+
files remain untracked across avg. enterprise
10Days
10Days
average time to detect a data exposure
€0M+
€0M+
average time to detect a data exposure
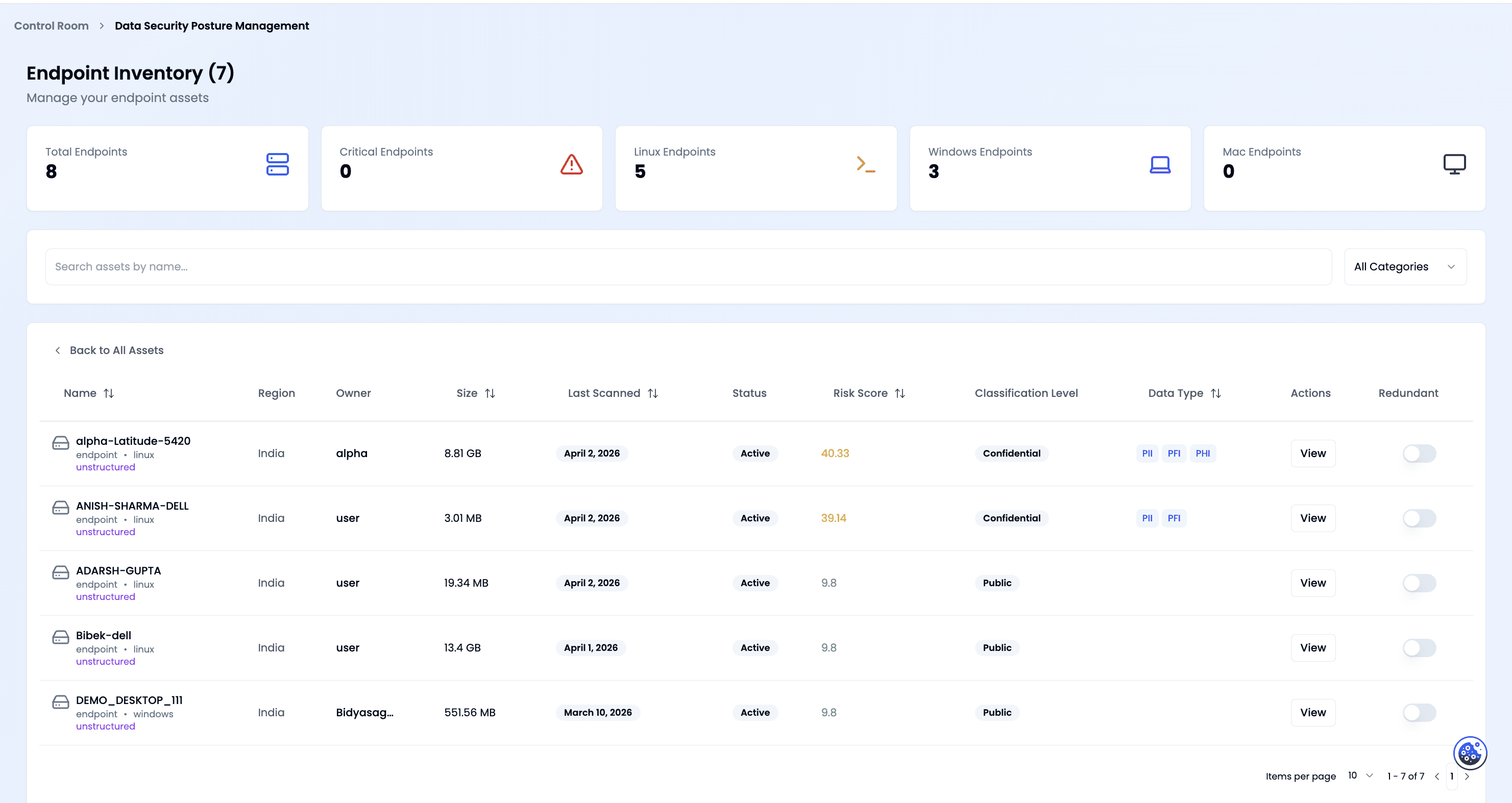
What GoTrust Endpoint Discovery Does
GoTrust Endpoint Discovery provides a comprehensive suite of capabilities designed to give your organization complete control over sensitive data on endpoints:

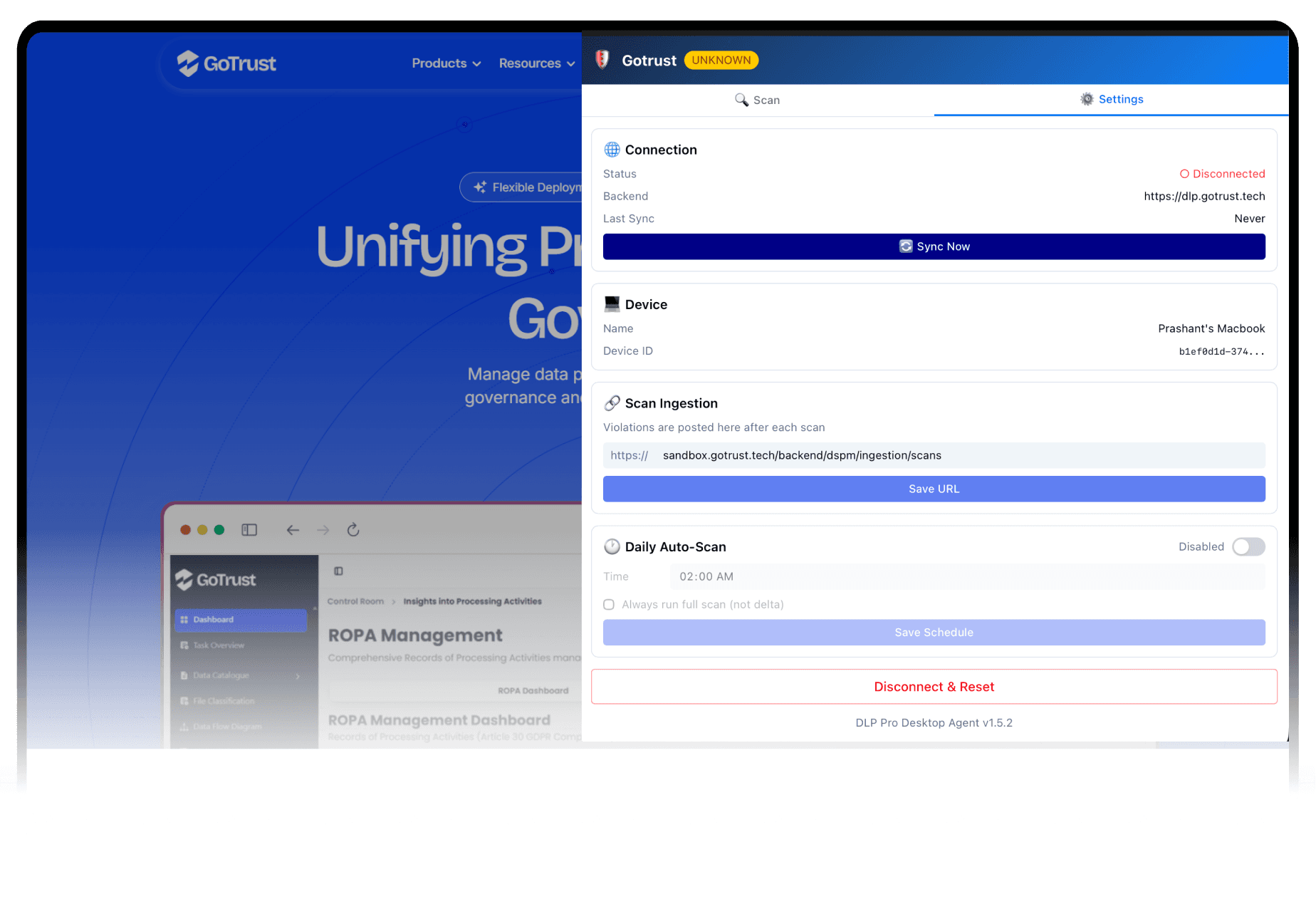
Automated Endpoint Scanning
Deploy lightweight agents to Windows, macOS, and Linux endpoints across your enterprise. Scans run on configurable schedules or on-demand, with minimal performance impact on end users.

Intelligent Data Classification
Leverage AI-powered classification to identify sensitive data categories including PII, financial records, health information, IP assets, and credentials — with pinpoint accuracy.

Precise Data Location Mapping
Get an exact, real-time map of where sensitive data resides — which devices, which folders, which users — down to the individual file level across your entire endpoint fleet.

Policy-Based Discovery Rules
Define custom discovery policies aligned to your specific compliance framework. Set risk thresholds, keyword lists, regex patterns, and file-type filters to tailor scans to your needs.

Risk Scoring & Prioritization
Every discovered data item is assigned an exposure risk score, enabling your team to prioritize remediation efforts where they matter most — not just where they are easiest.

Real-Time Alerts & Notifications
Receive instant alerts when high-risk data is discovered on endpoints, with contextual detail needed to take swift remediation action without delay.

Remediation Workflow Integration
Trigger automated or manual remediation workflows directly from discovery findings — encrypt, quarantine, delete, or escalate files based on configurable business rules.

Audit-Ready Compliance Reporting
Generate detailed reports on endpoint data exposure, discovery coverage, and remediation actions for regulatory audits, DPO reviews, and executive dashboards.
The GoTrust Endpoint Discovery Process
Step 1 — Deploy
Install the GoTrust lightweight endpoint agent via your existing MDM or endpoint management solution (SCCM, Jamf, Intune). Zero-touch deployment gets you operational across thousands of endpoints in hours, not weeks.
Step 2 — Discover
Agents conduct deep scans of local storage — including documents, databases, email archives, browser caches, cloud-sync folders, and removable media — using GoTrust's multi-layered detection engine combining pattern matching, machine learning, and contextual analysis.
Step 3 — Classify
Detected data is automatically classified using GoTrust's built-in taxonomy aligned to global regulations (GDPR Article 9, CCPA sensitive categories, HIPAA PHI, and more), or custom taxonomies you define for your organization.
Step 4 — Assess Risk
Each discovered data item is evaluated against your exposure risk framework — considering factors like data sensitivity, user access levels, encryption status, and device security posture — to generate a prioritized risk register.
Step 5 — Remediate
Act on findings directly from the GoTrust dashboard. Automatically encrypt sensitive files, trigger deletion workflows, notify data owners, or escalate to your DPO — all with a complete, timestamped audit trail for regulatory accountability.
Step 6 — Monitor & Report
Continuous monitoring ensures new data exposures are detected as they occur. Schedule automated compliance reports for regular review, and integrate GoTrust discovery data into your broader GRC and SIEM platforms via open APIs.
Who Benefits From GoTrust Endpoint Discovery?
IT Security Teams
Eliminate endpoint data blind spots that create breach exposure. Reduce the attack surface by identifying and remediating sensitive data on unprotected or non-compliant devices before adversaries can exploit them.
Legal & Compliance
Demonstrate due diligence in data governance during regulatory investigations. Produce evidence-backed audit reports showing your organization's proactive approach to data discovery and protection across all endpoints.
HR & Finance Ops
Ensure employee PII, payroll records, and financial documents saved locally on workstations are identified and protected. Avoid inadvertent non-compliance from decentralized data handling practices.
CISOs & CIOs
Gain executive-level visibility into enterprise-wide data exposure through GoTrust's intuitive dashboards. Make risk-informed decisions with real data on your endpoint exposure landscape.
M&A Due Diligence
During mergers and acquisitions, rapidly scan endpoint fleets of newly integrated organizations to assess inherited data privacy risk and accelerate compliance integration timelines.
Regulatory Frameworks Supported
GoTrust Endpoint Discovery is built to support compliance with the world's leading data privacy and protection regulations:
GDPR
of data breaches involve endpoint devices
CCPA / CPRA
California Privacy Laws
HIPAA
US Health Data Privacy
PDPB
India Personal Data Protection
ISO 27001
Information Security Mgmt
Our regulatory library is continuously updated as new frameworks emerge globally — ensuring your organization stays compliant today and tomorrow.
Why Choose GoTrust for Endpoint Discovery?
Designed for organizations managing thousands of distributed endpoints across multiple regions, offices, and remote environments.
GoTrust is built on a zero-trust, privacy-by-design foundation. Scan results are processed securely and never leave your environment without explicit authorization.
Our lightweight agent consumes less than 1% of CPU and memory during scans, ensuring end-user productivity is never compromised.
Endpoint Discovery integrates natively with the full GoTrust suite — including Data Mapping, DSAR Management, Consent Management, and Breach Response modules.
Most organizations achieve full endpoint coverage and their first discovery report within 48 hours of deployment.
Backed by GoTrust's in-house team of data privacy specialists, legal experts, and security engineers available to support your compliance journey.



Talk To Our Expert
Schedule a session with our team to see how GoTrust unifies consent, privacy automation, DSPM, and governance into one intelligent compliance platform.






